You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
Identical laptop's ip seen from Different servers
- Thread starter gdf
- Start date
Did your IP address change between the time you logged in earlier and you logged in now? Even from the same ISP, addresses can vary greatly.
That's the most simple explanation.
Were you using a VPN when connected last time?
Did you do geolocation on the unknown address?
That's the most simple explanation.
Were you using a VPN when connected last time?
Did you do geolocation on the unknown address?
Well, someone accessed it with an unknown IP address. That's something you can be pretty sure of.
I'd geolocate the IP address and check other logs to see what signs they left behind. I'd do my bst to gie a forensic examination before wiping it clean and restoring from clean backups. If no such backups exist, I'd start again - making sure to follow best-practices with regards to security. (Stuff like disabling password login and requiring a key to get into the server.)
I'd geolocate the IP address and check other logs to see what signs they left behind. I'd do my bst to gie a forensic examination before wiping it clean and restoring from clean backups. If no such backups exist, I'd start again - making sure to follow best-practices with regards to security. (Stuff like disabling password login and requiring a key to get into the server.)
Condobloke
Well-Known Member
@KGIII ....Just to add to your workload, David, a blurb about how to geolocate an IP address may be an idea?
And....
And....
?Stuff like disabling password login andrequiring a key to get into the server.)
It's pretty basic to geolocate an IP address. Just pick a service and go:
 www.iplocation.net
www.iplocation.net
(etc... there's tons of sites for this)
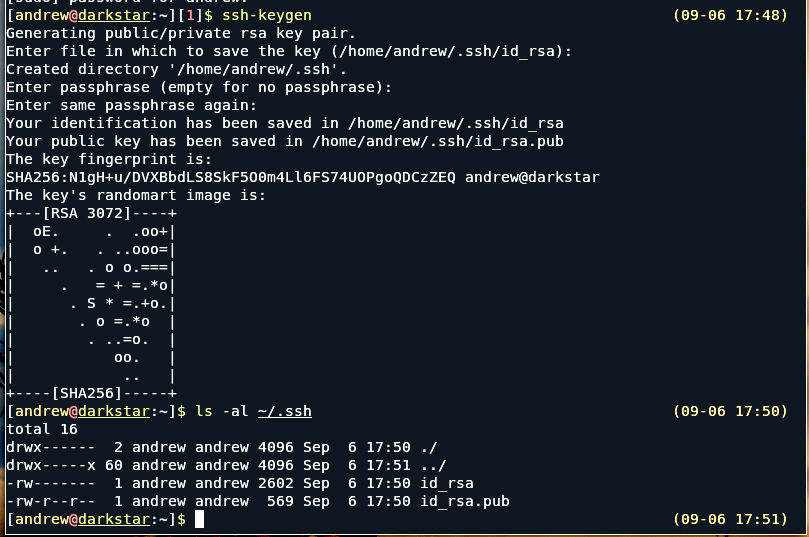
You can disable password login with SSH.

 linuxhandbook.com
linuxhandbook.com
See also:
 linux-tips.us
linux-tips.us
A properly secured key is a zillion times better than a password. An improperly secured key is still probably better security than a password. You can mostly deal with brute-force attacks with firejail, but a properly secured key is a zillion times better. It's not even hard to secure it. Keep it where it should be and keep a backup on a thumbdrive that you don't walk around with. Logout of your device when you walk away from it, at least lock the screen.
IP Address Lookup | Geolocation
Lookup your public IPv4 or IPv6 address and where are you located? Find a geolocation of your IP address including latitude, longitude, city, region and country.
(etc... there's tons of sites for this)
You can disable password login with SSH.

How to Disable SSH Login With Password
One of the basic SSH hardening step is to disable password based SSH login. This reduces the risk of a brute force attack on your Linux server.
 linuxhandbook.com
linuxhandbook.com
See also:
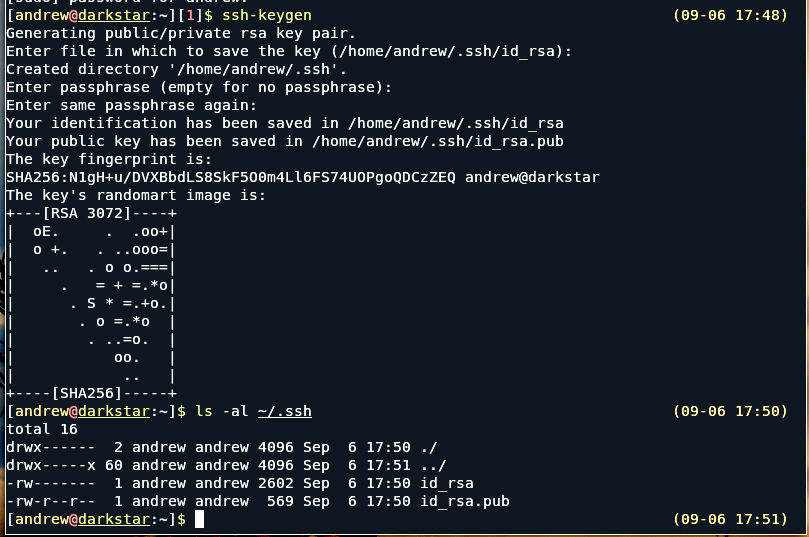
Guest Article: What Are SSH Keys? • Linux Tips
The following article is a guest-written article from Andy Brooks (aka captain-sensible) about SSH keys.
A properly secured key is a zillion times better than a password. An improperly secured key is still probably better security than a password. You can mostly deal with brute-force attacks with firejail, but a properly secured key is a zillion times better. It's not even hard to secure it. Keep it where it should be and keep a backup on a thumbdrive that you don't walk around with. Logout of your device when you walk away from it, at least lock the screen.

