Hello dear, I'm trying to use GDB (GNU Debbugger) to debug the execution of Adobe Reader 8 installed on Windows XP SP3 through GDB installaed with MinGW.
I tried to open the file using adobe reader in the cmd with the intent to fine a command line valid for gdb and i found the following:
That works becouse it will open correctly the file using Adobe Reader, but if i try to use this command into gdb invocation it will crash.
At the moment I'm using the following command line:
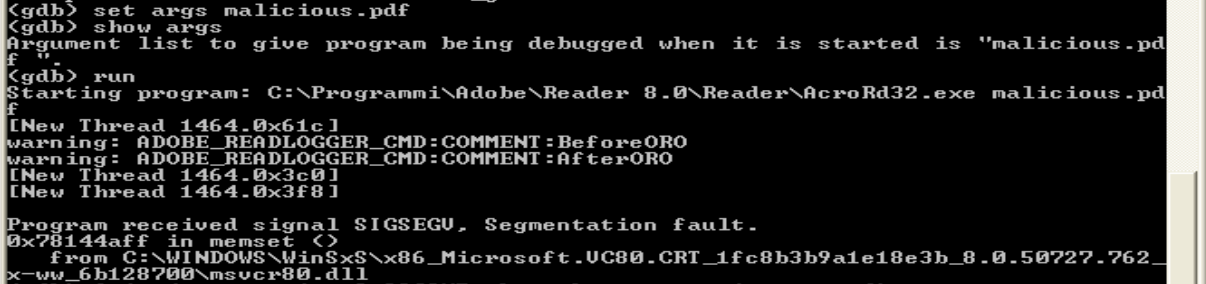
Then i use set args malicious.pdf that permite me to pass the malicious file (the pdf) as an argument readable from Adobe Reader at execution time.
The output that i receive is the following
Then i see an Adobe Reader window but not loaded completly.
The pdf file is generated with the use of metasploit exploit exploit/windows/fileformat/adobe_utilprintf
I tried to open the file using adobe reader in the cmd with the intent to fine a command line valid for gdb and i found the following:
"C:\Programmi\Adobe\Reader 8.0\Reader\AcroRd32.exe" "C:\Documents and Settings\aleff\Desktop\malicious.pdf"
That works becouse it will open correctly the file using Adobe Reader, but if i try to use this command into gdb invocation it will crash.
At the moment I'm using the following command line:
C:\MinGW\bin\gdb.exe "C:\Programmi\Adobe\Reader 8.0\Reader\AcroRd32.exe"
Then i use set args malicious.pdf that permite me to pass the malicious file (the pdf) as an argument readable from Adobe Reader at execution time.
The output that i receive is the following
Then i see an Adobe Reader window but not loaded completly.
The pdf file is generated with the use of metasploit exploit exploit/windows/fileformat/adobe_utilprintf

