D
DevynCJohnson
Guest
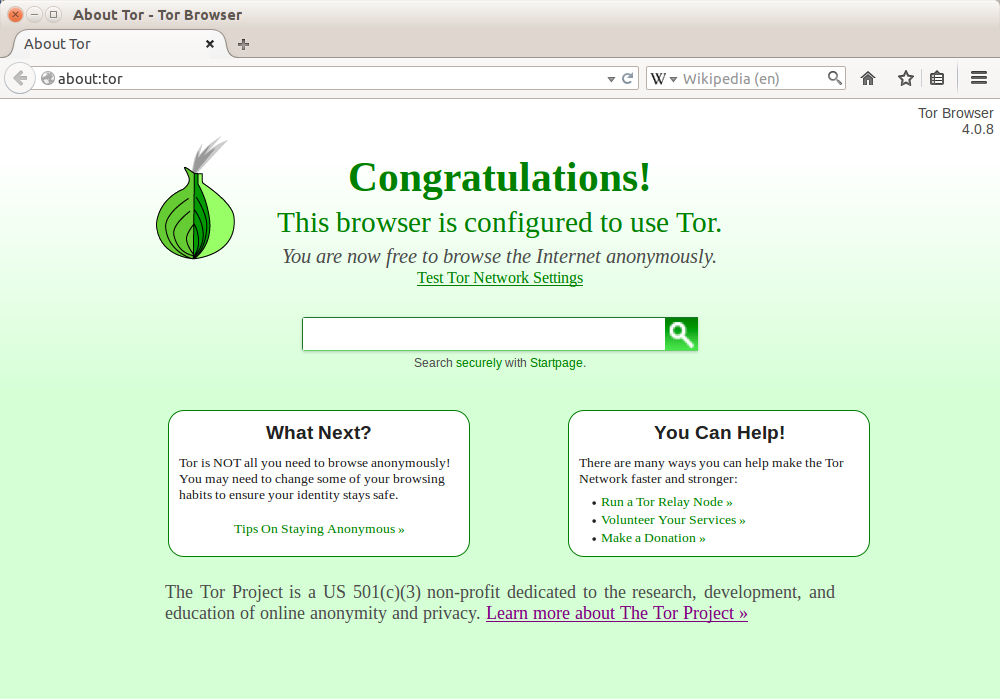
The Internet is a large place that is becoming increasingly popular and larger. The Internet provides many benefits and services. For instance, people from nearly anywhere in the world can communicate via Skype, Google+, Twitter, Facebook, and many other forums and social sites. People can also shop, learn, play, etc. However, like the physical world, people may be concerned about privacy and security. Thankfully, Tor offers great security, privacy, and more.
Getting Tor
To install the Tor Browser on Ubuntu, add the below PPA.
Next, run the below command with Root privileges. If Tor is in the default repos of other Debian-based distros, then the below command may work without the above PPA.
For Fedora, add the Tor repo by creating a file (/etc/yum.repos.d/tor.repo) and pacing the below code in the file. Afterwards, execute “yum install tor” in a command-line with Root privileges.
Many installation guides can be found at https://www.torproject.org/docs/installguide.html
About Tor
Tor is open-source freeware written is C. The browser is available for all systems including Windows, Linux (and Android), OS X, iOS, and various Unixoid systems. Tor is an acronym for "The Onion Router". Tor networks are made up of "Tor Relays". When a Tor client connects to a server, a random path between the client and server is created among the Tor relays. The data is encrypted many times. Each relay decrypts the data once to get information as to where to send the data next. Then, the next relay decrypts another layer and sends the data to the next relay until the data reaches the client or server. Since the data is encrypted multiple times, the data is often compared to an onion with many layers (hence the name). This layered concept is called "Onion Routing".
NOTE: Tor relays are sometimes called Tor servers or Onion Routers.
Because of the way Tor operates, this provides users with additional security and privacy from black-hat hackers and cruel governments. Some countries restrict the sites users may view. Other countries penalize users from using certain sites. Tor provides people with the freedom they deserve. For example, China restricts its citizens from viewing Tibetan material. People that see nothing wrong with the peaceful Tibetan practices may wish to learn more about such banned subjects. Tor offers freedom that the politicians fail to give to their citizens.
FUN FACT: Edward Snowden informed the Guardian and the Washington Post about PRISM by using the Tor web-browser in June 2013.
Not only does Tor provide anonymous web browsing, but it also acts as a gateway to the Dark Web (also called the Deepnet, Deep Web or Dark Internet). According to many sources (like The Guardian - http://www.theguardian.com/) the Darknet is larger than the Surface Internet (the Internet people are familiar with). The Dark Web is not accessible to regular web browsers like Mozilla Firefox or Google Chrome (an exception is mentioned later). Rather, the Dark Web is accessible via the Tor Web-browser.
NOTE: The "Darknet" is the part of the Deep Web accessible by Tor and Onion routing. Other subdivisions exist in the Deep Web.
The Darknet
The Darknet is designed a little differently than the Surface Internet. Many websites on the Darknet use domain names that are 16-character hashes (random characters) that make up an 80-bit number in base32 rather than purposely designed domain names (like "Wikipedia.org" or "DCJTech.info"). Also, many website domain names (or addresses) end in ".onion" instead of ".com" or ".net". JavaScript is typically disabled in the Tor browser because Darknet websites are not supposed to use JavaScript. This helps with security and privacy.
".onion" is not an official top-level-domain. However, the Darknet uses Tor DNS servers rather than Internet DNS servers. Other possible top-level-domains on the Dark Web include ".bitnet", ".i2p", ".bit", ".exit", and ".uucp".
Regular web-browsers can access the Dark Web via Tor2Web (https://www.tor2web.org/), but security and privacy is not guaranteed.
The Darknet has its own set of search engines since Google and Bing are designed for the Surface Internet. On the Darknet, the search engines only search the sites that want to be searched. Three popular search engines for the Darknet are Torch (http://xmh57jrzrnw6insl.onion/), DuckDuckGo (http://3g2upl4pq6kufc4m.onion/), and Tor Search (http://hss3uro2hsxfogfq.onion/) which is also called "Not Evil".
Other Darknet websites include Facebook's Onion Portal (https://www.facebookcorewwwi.onion/) and The Hidden Wiki (http://kpvz7kpmcmne52qf.onion). A list of more Darknet weblinks can be found at The Hidden Wiki on the Surface Internet (http://thehiddenwiki.org/).
A large list of Tor (Onion) I2P, and other DarkWeb links can be found at http://dcjtech.info/topic/darkweb-link-list/
Extras
To disable the webcam on a Linux system, run the below code with Root privileges.
Further Reading
Getting Tor
To install the Tor Browser on Ubuntu, add the below PPA.
Code:
add-apt-repository ppa:webupd8team/tor-browserNext, run the below command with Root privileges. If Tor is in the default repos of other Debian-based distros, then the below command may work without the above PPA.
Code:
apt-get update
apt-get install tor-browserFor Fedora, add the Tor repo by creating a file (/etc/yum.repos.d/tor.repo) and pacing the below code in the file. Afterwards, execute “yum install tor” in a command-line with Root privileges.
Code:
[Tor]
name=Tor Project Repo
baseurl=http://deb.torproject.org/torproject.org/rpm/fc/20/$basearch/
gpgcheck=1
enabled=1
gpgkey=http://deb.torproject.org/torproject.org/rpm/RPM-GPG-KEY-torproject.org.ascMany installation guides can be found at https://www.torproject.org/docs/installguide.html
About Tor
Tor is open-source freeware written is C. The browser is available for all systems including Windows, Linux (and Android), OS X, iOS, and various Unixoid systems. Tor is an acronym for "The Onion Router". Tor networks are made up of "Tor Relays". When a Tor client connects to a server, a random path between the client and server is created among the Tor relays. The data is encrypted many times. Each relay decrypts the data once to get information as to where to send the data next. Then, the next relay decrypts another layer and sends the data to the next relay until the data reaches the client or server. Since the data is encrypted multiple times, the data is often compared to an onion with many layers (hence the name). This layered concept is called "Onion Routing".
NOTE: Tor relays are sometimes called Tor servers or Onion Routers.
Because of the way Tor operates, this provides users with additional security and privacy from black-hat hackers and cruel governments. Some countries restrict the sites users may view. Other countries penalize users from using certain sites. Tor provides people with the freedom they deserve. For example, China restricts its citizens from viewing Tibetan material. People that see nothing wrong with the peaceful Tibetan practices may wish to learn more about such banned subjects. Tor offers freedom that the politicians fail to give to their citizens.
FUN FACT: Edward Snowden informed the Guardian and the Washington Post about PRISM by using the Tor web-browser in June 2013.
Not only does Tor provide anonymous web browsing, but it also acts as a gateway to the Dark Web (also called the Deepnet, Deep Web or Dark Internet). According to many sources (like The Guardian - http://www.theguardian.com/) the Darknet is larger than the Surface Internet (the Internet people are familiar with). The Dark Web is not accessible to regular web browsers like Mozilla Firefox or Google Chrome (an exception is mentioned later). Rather, the Dark Web is accessible via the Tor Web-browser.
NOTE: The "Darknet" is the part of the Deep Web accessible by Tor and Onion routing. Other subdivisions exist in the Deep Web.
The Darknet
The Darknet is designed a little differently than the Surface Internet. Many websites on the Darknet use domain names that are 16-character hashes (random characters) that make up an 80-bit number in base32 rather than purposely designed domain names (like "Wikipedia.org" or "DCJTech.info"). Also, many website domain names (or addresses) end in ".onion" instead of ".com" or ".net". JavaScript is typically disabled in the Tor browser because Darknet websites are not supposed to use JavaScript. This helps with security and privacy.
".onion" is not an official top-level-domain. However, the Darknet uses Tor DNS servers rather than Internet DNS servers. Other possible top-level-domains on the Dark Web include ".bitnet", ".i2p", ".bit", ".exit", and ".uucp".
Regular web-browsers can access the Dark Web via Tor2Web (https://www.tor2web.org/), but security and privacy is not guaranteed.
The Darknet has its own set of search engines since Google and Bing are designed for the Surface Internet. On the Darknet, the search engines only search the sites that want to be searched. Three popular search engines for the Darknet are Torch (http://xmh57jrzrnw6insl.onion/), DuckDuckGo (http://3g2upl4pq6kufc4m.onion/), and Tor Search (http://hss3uro2hsxfogfq.onion/) which is also called "Not Evil".
Other Darknet websites include Facebook's Onion Portal (https://www.facebookcorewwwi.onion/) and The Hidden Wiki (http://kpvz7kpmcmne52qf.onion). A list of more Darknet weblinks can be found at The Hidden Wiki on the Surface Internet (http://thehiddenwiki.org/).
A large list of Tor (Onion) I2P, and other DarkWeb links can be found at http://dcjtech.info/topic/darkweb-link-list/
Extras
To disable the webcam on a Linux system, run the below code with Root privileges.
Code:
modprobe -r uvcvideoFurther Reading
- Official Website - https://www.torproject.org/
- General Tor Info - http://lifehacker.com/what-is-tor-and-should-i-use-it-1527891029
- Electronic Frontier Foundation (Tor and HTTPS Article) - https://www.eff.org/pages/tor-and-https
- Info on the NSA's illegal mass surveillance program - https://www.eff.org/nsa-spying
- Internet Censorship and Circumvention - http://www.linux.org/threads/internet-censorship-and-circumvention.8095/
- The Many Sides of the Internet: Arpanet, Darknet, and Others - http://www.linux.org/threads/the-many-sides-of-the-internet-arpanet-darknet-and-others.8389/
Attachments
Last edited:


