I hope you enjoy the articles for the LFCS Certification. If you have been following along using VirtualBox to go through the articles, then you will be ready for this one. If you are jumping into this one and not doing the previous one, Turning a System into a Router, then you need to go back to it and perform the steps before you start this article.
Be very sure you have completed and understood the previous article before starting this one. This article continues from the previous one and all steps are necessary.
Starting the Firewalld Service
Firewalld is a service that works similarly to the iptables command. The two commands perform the same functions, but firewalld is a little easier to use.
First thing, for Ubuntu systems, you need to install firewalld with the command:
sudo apt install firewalld -y
After installing it, Ubuntu will start the service and enable an auto-start on a reboot.
Our CentOS systems have already installed firewalld, but we need to start the service. Before we start the service, we can check the service with the command:
firewall-cmd --state
The response should be ‘not running’, but if your system has it running already, then you do not need to start it.
To start the service, use the commands:
sudo systemctl start firewalld
sudo systemctl enable firewalld
These two commands should start the service and set it up to start at boot. Once started, you can check the state again to verify the srvice is started.
NOTE: The service needs to be started on Server2, which was enabled as a routing system.
Zones
A zone is a configuration for a specific area that is assigned to a Network Interface Card (NIC).
To see a list of zones, use the command:
firewall-cmd --get-zones
The returned zones for both Ubuntu and CentOS are:
block dmz drop external home internal public trusted work
To see the default zone for your system, use the command:
firewall-cmd --get-default-zone
The result should be ‘public’. ‘Public’ is the default zone for all network adapters on systems. We will move the settings from one zone to another and set up each adapter in a specific zone. Any changes made to a zone, without specifying which zone, will take place to the default of ‘Public’ until we change the default.
To see the zone that the interfaces are in, use the command:
firewall-cmd --get-active-zones
My result from the command is:
public
interfaces: enp0s3 enp0s8
You can see that both network cards, ‘enp0s3’ and ‘enp0s8’, are in the Public zone.
To see what is enabled in ‘Public’ and the cards in the zone, use:
firewall-cmd --list-all
You can see the results from the command in Figure 1. If your results do not show that the ‘MASQUERADE’ value is ‘yes’, then you can set the value with the command:
firewall-cmd --add-masquerade --permanent
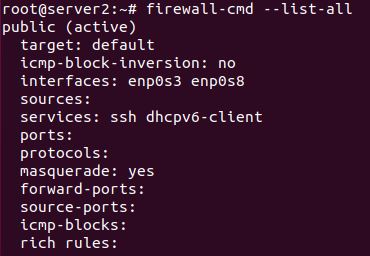
FIGURE 1
If you run the command to check the values of ‘MASQUERADE’, it will still be set to ‘no’ until you reload the configuration with the command:
firewall-cmd --reload
After reloading the configuration, the command 'firewall-cmd --list-all' should show that the value is 'yes'.
So, let’s look at changing the default zone to ‘Internal’. The command is:
firewall-cmd --set-default-zone=internal
If we look at the ‘Internal’ zone settings, with the command ‘firewall-cmd –list-all’, you should see something similar to Figure 2.
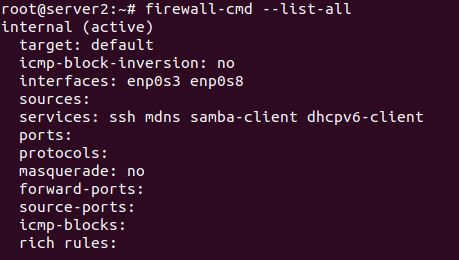
FIGURE 2
Let’s look at moving the ‘services’ from the ‘Public’ zone to the ‘Internal’ zone. Let’s first remove the services from ‘Internal’.
firewall-cmd –permanent --remove-service=ssh
The command will remove one service, but you can remove multiple services by placing them in curly brackets and separating them with commas and no spaces, such as in:
firewall-cmd --permanent --remove-service={ssh,mdns,samba-client,dhcpv6-client}
If you perform a reload and then list all, you’ll see that the services are all gone for the default zone.
NOTE: Remember that we didn’t need to specify the zone since we were using the default zone of ‘Internal’.
Now, let’s copy over the services from ‘Public’ to ‘Internal’. The list from ‘Public’ is ‘dhcpv6-client, mdns, ntp, ssh’. Like before, we can add one service at a time with the parameter ‘--add=service’, or we can add multiples with curly brackets again. Try the following:
firewall-cmd --permanent --add-service={dhcpv6-client,mdns,ntp,ssh}
As usual, perform a reload before you list all. The services are now in the 'Internal' zone. We can delete the services from the 'Public' zone with:
firewall-cmd --permanent --remove-service={dhcpv6-client,mdns,ntp,ssh} --zone=public
Reload and list all to see the changes for the ‘Public’ zone.
Both network adapters are in the 'Internal' zone, but one needs to be moved to the 'External' zone. On my systems for both Ubuntu and CentOS, the network adapter ‘enp0s3’ is set for the network with all my other devices. I want to then move ‘enp0s3’ to the ‘External’ zone for both systems.
firewall-cmd --permanent --zone=external --add-interface=enp0s3
Reload as usual. For the ‘External’ zone, the only service enabled is ‘ssh’. You can add other services as you need.
Adding a Service
Let’s say you work for a company that has a program that they use that has specific port requirements. You cannot easily use an existing service name, such as ‘ssh’ or the like.
If your company program name is ‘DatabaseMGR’ and uses Ports 9005 for TCP, 9006 for TCP and 9010 for UDP, we can create a service entry for the firewall.
If you look in '/usr/lib/firewalld/services/', you will see the general services available. We create new services in '/etc/firewalld/services/' when we create them. The last folder should be empty unless you have created some services already. To create a service, use the command:
firewall-cmd --permanent --new-service=“DatabaseMGR”
NOTE: Replace the curly double quotes with straight double quotes in the terminal.
Change to the directory and we need to restore the SELinux security to the file. For Ubuntu, you’ll need to ‘sudo apt install policycoreutils’.
Perform the following two commands:
restorecon DatabaseMGR.xml
chmod 640 DatabaseMGR.xml
You need to edit the ‘DatabaseMGR.xml’ file and you should see the following:
<?xml version="1.0" encoding="utf-8"?>
<service>
</service>
You’ll need to change the file to:
<?xml version="1.0" encoding="utf-8"?>
<service>
<short>DatabaseMGR</short>
<port protocol="tcp" port="9005"/>
<port protocol="tcp" port="9006"/>
<port protocol="udp" port="9010"/>
</service>
Save the file and we can add it to the ‘External’ zone with the command:
firewall-cmd --permanent --add-service=DatabaseMGR --zone=external
Reload and list the information for the ‘External’ zone and you should see the service listed.
Conclusion
You should see that using the ‘firewall-cmd’ is not a hard program to use. You can control the firewall with ease from the command line.
Practice these steps in a terminal on a VirtualBox Machine, or a real system if available.
Be very sure you have completed and understood the previous article before starting this one. This article continues from the previous one and all steps are necessary.
Starting the Firewalld Service
Firewalld is a service that works similarly to the iptables command. The two commands perform the same functions, but firewalld is a little easier to use.
First thing, for Ubuntu systems, you need to install firewalld with the command:
sudo apt install firewalld -y
After installing it, Ubuntu will start the service and enable an auto-start on a reboot.
Our CentOS systems have already installed firewalld, but we need to start the service. Before we start the service, we can check the service with the command:
firewall-cmd --state
The response should be ‘not running’, but if your system has it running already, then you do not need to start it.
To start the service, use the commands:
sudo systemctl start firewalld
sudo systemctl enable firewalld
These two commands should start the service and set it up to start at boot. Once started, you can check the state again to verify the srvice is started.
NOTE: The service needs to be started on Server2, which was enabled as a routing system.
Zones
A zone is a configuration for a specific area that is assigned to a Network Interface Card (NIC).
To see a list of zones, use the command:
firewall-cmd --get-zones
The returned zones for both Ubuntu and CentOS are:
block dmz drop external home internal public trusted work
To see the default zone for your system, use the command:
firewall-cmd --get-default-zone
The result should be ‘public’. ‘Public’ is the default zone for all network adapters on systems. We will move the settings from one zone to another and set up each adapter in a specific zone. Any changes made to a zone, without specifying which zone, will take place to the default of ‘Public’ until we change the default.
To see the zone that the interfaces are in, use the command:
firewall-cmd --get-active-zones
My result from the command is:
public
interfaces: enp0s3 enp0s8
You can see that both network cards, ‘enp0s3’ and ‘enp0s8’, are in the Public zone.
To see what is enabled in ‘Public’ and the cards in the zone, use:
firewall-cmd --list-all
You can see the results from the command in Figure 1. If your results do not show that the ‘MASQUERADE’ value is ‘yes’, then you can set the value with the command:
firewall-cmd --add-masquerade --permanent
FIGURE 1
If you run the command to check the values of ‘MASQUERADE’, it will still be set to ‘no’ until you reload the configuration with the command:
firewall-cmd --reload
After reloading the configuration, the command 'firewall-cmd --list-all' should show that the value is 'yes'.
So, let’s look at changing the default zone to ‘Internal’. The command is:
firewall-cmd --set-default-zone=internal
If we look at the ‘Internal’ zone settings, with the command ‘firewall-cmd –list-all’, you should see something similar to Figure 2.
FIGURE 2
Let’s look at moving the ‘services’ from the ‘Public’ zone to the ‘Internal’ zone. Let’s first remove the services from ‘Internal’.
firewall-cmd –permanent --remove-service=ssh
The command will remove one service, but you can remove multiple services by placing them in curly brackets and separating them with commas and no spaces, such as in:
firewall-cmd --permanent --remove-service={ssh,mdns,samba-client,dhcpv6-client}
If you perform a reload and then list all, you’ll see that the services are all gone for the default zone.
NOTE: Remember that we didn’t need to specify the zone since we were using the default zone of ‘Internal’.
Now, let’s copy over the services from ‘Public’ to ‘Internal’. The list from ‘Public’ is ‘dhcpv6-client, mdns, ntp, ssh’. Like before, we can add one service at a time with the parameter ‘--add=service’, or we can add multiples with curly brackets again. Try the following:
firewall-cmd --permanent --add-service={dhcpv6-client,mdns,ntp,ssh}
As usual, perform a reload before you list all. The services are now in the 'Internal' zone. We can delete the services from the 'Public' zone with:
firewall-cmd --permanent --remove-service={dhcpv6-client,mdns,ntp,ssh} --zone=public
Reload and list all to see the changes for the ‘Public’ zone.
Both network adapters are in the 'Internal' zone, but one needs to be moved to the 'External' zone. On my systems for both Ubuntu and CentOS, the network adapter ‘enp0s3’ is set for the network with all my other devices. I want to then move ‘enp0s3’ to the ‘External’ zone for both systems.
firewall-cmd --permanent --zone=external --add-interface=enp0s3
Reload as usual. For the ‘External’ zone, the only service enabled is ‘ssh’. You can add other services as you need.
Adding a Service
Let’s say you work for a company that has a program that they use that has specific port requirements. You cannot easily use an existing service name, such as ‘ssh’ or the like.
If your company program name is ‘DatabaseMGR’ and uses Ports 9005 for TCP, 9006 for TCP and 9010 for UDP, we can create a service entry for the firewall.
If you look in '/usr/lib/firewalld/services/', you will see the general services available. We create new services in '/etc/firewalld/services/' when we create them. The last folder should be empty unless you have created some services already. To create a service, use the command:
firewall-cmd --permanent --new-service=“DatabaseMGR”
NOTE: Replace the curly double quotes with straight double quotes in the terminal.
Change to the directory and we need to restore the SELinux security to the file. For Ubuntu, you’ll need to ‘sudo apt install policycoreutils’.
Perform the following two commands:
restorecon DatabaseMGR.xml
chmod 640 DatabaseMGR.xml
You need to edit the ‘DatabaseMGR.xml’ file and you should see the following:
<?xml version="1.0" encoding="utf-8"?>
<service>
</service>
You’ll need to change the file to:
<?xml version="1.0" encoding="utf-8"?>
<service>
<short>DatabaseMGR</short>
<port protocol="tcp" port="9005"/>
<port protocol="tcp" port="9006"/>
<port protocol="udp" port="9010"/>
</service>
Save the file and we can add it to the ‘External’ zone with the command:
firewall-cmd --permanent --add-service=DatabaseMGR --zone=external
Reload and list the information for the ‘External’ zone and you should see the service listed.
Conclusion
You should see that using the ‘firewall-cmd’ is not a hard program to use. You can control the firewall with ease from the command line.
Practice these steps in a terminal on a VirtualBox Machine, or a real system if available.

