Recently I came across a few HP G8 servers at work that still had older iLO 4 firmware versions installed. This presented a problem because in August of 2017 there was a vulnerability patched which would allow a remote attacker to create their own Admin level user and enter the system.
Yes, there is a script currently on github which allows you to do this on an unpatched iLO.
This would allow them console level of the server which means they would then have complete control over the Linux/OS side of things after they rebooted in single user mode and changed the root password.
Background on the security vulnerability:
News article: https://www.bleepingcomputer.com/ne...ion-on-hpe-ilo4-servers-with-29-a-characters/
HPE Doc: https://support.hpe.com/hpsc/doc/public/display?docId=emr_na-hpesbhf03769en_us
CVE Details: https://nvd.nist.gov/vuln/detail/CVE-2017-12542
Testing vulnerability:
The vulnerability was fixed in version 2.54, so any version of iLO 4 that is 2.53 or earlier is affected.
To test against your iLO, run the following curl command, replacing xxx.xxx.xxx.xxx with the iLO IP you are testing against.
Testing with the curl command on a vulnerable server. You can see it listing out the user accounts:
Patching the system:
Testing once again after the firmware update. Now, we see '401 unauthorized' as well as no user data:
Yes, there is a script currently on github which allows you to do this on an unpatched iLO.
This would allow them console level of the server which means they would then have complete control over the Linux/OS side of things after they rebooted in single user mode and changed the root password.
Background on the security vulnerability:
News article: https://www.bleepingcomputer.com/ne...ion-on-hpe-ilo4-servers-with-29-a-characters/
HPE Doc: https://support.hpe.com/hpsc/doc/public/display?docId=emr_na-hpesbhf03769en_us
CVE Details: https://nvd.nist.gov/vuln/detail/CVE-2017-12542
Testing vulnerability:
The vulnerability was fixed in version 2.54, so any version of iLO 4 that is 2.53 or earlier is affected.
To test against your iLO, run the following curl command, replacing xxx.xxx.xxx.xxx with the iLO IP you are testing against.
Code:
curl -k -i -H "Connection: AAAAAAAAAAAAAAAAAAAAAAAAAAAAA" https://xxx.xxx.xxx.xxx/rest/v1/AccountService/Accounts- If the curl command returns with 'HTTP/1.1 200 OK' followed by various information like usernames, etc.. then it is vulnerable.
- If the curl command returns with 'HTTP/1.1 401 Unauthorized' followed by not much information, it is patched.
- Download current iLO firmware version (v.2.60 / filename: CP033806.scexe for RHEL/CentOS 6)
https://support.hpe.com/hpsc/swd/pu...=MTX_439693a1acbb434994ccb76e31&swEnvOid=4184 - Upload iLO firmware file to server
Code:scp /path/to/CP033806.scexe user@host:/var/tmp/ - As root, run firmware file:
Code:sh /var/tmp/CP033806.scexe - Read, follow and answer the prompts to update the firmware from 2.xx to 2.60.
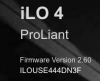
- Open a web browser and visit the iLO IP (https://xxx.xxx.xxx.xxx) to confirm 2.60 version
- Run curl command (above) to test vulnerability
Testing with the curl command on a vulnerable server. You can see it listing out the user accounts:
Code:
[rob@home ~]$ curl -k -i -H "Connection: AAAAAAAAAAAAAAAAAAAAAAAAAAAAA" https://xxx.xxx.xxx.xxx/rest/v1/AccountService/Accounts
HTTP/1.1 200 OK
Allow: GET, HEAD, POST
Cache-Control: no-cache
Content-length: 670
Content-type: application/json
Date: Tue, 10 Jul 2018 17:31:22 GMT
ETag: W/"AXXXXXXC"
Server: HP-iLO-Server/1.30
X_HP-CHRP-Service-Version: 1.0.3
{"Description":"iLO User Accounts","Items":[{"Description":"iLO User Account","Name":"User Account","Oem":{"Hp":{"LoginName":"Administrator","Privileges":{"LoginPriv":true,"RemoteConsolePriv":true,"UserConfigPriv":true,"VirtualMediaPriv":true,"VirtualPowerAndResetPriv":true,"iLOConfigPriv":true},"Type":"HpiLOAccount.0.9.5"}},"Password":null,"Type":"ManagerAccount.0.9.5","UserName":"Administrator","links":{"self":{"href":"/rest/v1/AccountService/Accounts/2"}}}],"MemberType":"ManagerAccount.0","Name":"Accounts","Total":1,"Type":"Collection.0.9.5","links":{"Member":[{"href":"/rest/v1/AccountService/Accounts/2"}],"self":{"href":"/rest/v1/AccountService/Accounts"}}}Patching the system:
Code:
[root@servername ~]# sh /var/tmp/CP033806.scexe
FLASH_iLO4 v1.17 for Linux (Sep 30 2015)
(C) Copyright 2002, 2015 Hewlett-Packard Enterprise Development Company, L.P.
Firmware image: ilo4_260.bin
Current iLO 4 firmware version 2.02; Serial number XXXXXXXXXX
Component XML file: CP033806.xml
CP033806.xml reports firmware version 2.60
This operation will update the firmware on the
iLO 4 in this server with version 2.60.
Continue (y/N)?y
Current firmware is 2.02 (Sep 05 2014 00:00:00)
Firmware image is 0x1001b1c(16784156) bytes
Committing to flash part...
******** DO NOT INTERRUPT! ********
Flashing is underway... 100 percent programmed. \
Succeeded.
***** iLO 4 reboot in progress (may take more than 60 seconds.)
***** Please ignore console messages, if any.
iLO 4 reboot completed.Testing once again after the firmware update. Now, we see '401 unauthorized' as well as no user data:
Code:
[rob@home ~]$ curl -k -i -H "Connection: AAAAAAAAAAAAAAAAAAAAAAAAAAAAA" https://xxx.xxx.xxx.xxx/rest/v1/AccountService/Accounts
HTTP/1.1 401 Unauthorized
Content-Type: application/json
Content-Length: 253
Date: Tue, 10 Jul 2018 17:41:53 GMT
X-Frame-Options: sameorigin
{"Messages":[{"MessageID":"Base.0.10.NoValidSession"}],"Type":"ExtendedError.1.0.0","error":{"@Message.ExtendedInfo":[{"MessageID":"Base.0.10.NoValidSession"}],"code":"iLO.0.10.ExtendedInfo","message":"See @Message.ExtendedInfo for more information."}}Attachments
Last edited: