In previous articles I discussed the installation and basic use of libvirt. I also covered the libvirt Graphical User Interface (GUI) called Virt-Manager.
Installation - https://www.linux.org/threads/virtualization-–-libvirt.4496/
GUI - https://www.linux.org/threads/virtualization-–-libvirt-gui.4497/
This article will cover more details of the configuration on various topics that aren’t obvious to set.
‘virsh’
The way to change some underlying settings for a Virtual Client is to use ‘virsh’. The command ‘virsh’ is run from a Terminal.
Once you start ‘virsh’ then you are in the ‘virsh’ editor. When editing the Virtual Client settings the default editor is ‘vi’, but this can be changed to your personal preference.
Let’s say you want the default editor to be ‘leafpad’. The command to run would be:
export EDITOR=leafpad
NOTE: When you reboot the system then the setting reverts back to the default.
Let’s make the default permanent. To make the settings permanent we need to have the environment variable set at boot time.
Open a Terminal and type the command ‘sudo leafpad /etc/environment’. Change the editor from ‘leafpad’ to your preferred editor by replacing the command to start the editor. Once the ‘environment’ file is opened you need to go to the last line and enter ‘EDITOR=leafpad’. Again, change the editor name to your preferred text editor. Save the changes and close the editor.
To make the settings take effect immediately and not require a reboot enter the command ‘source /etc/environment’.
Now you can execute the command ‘echo $EDITOR’ to see that the entry is set to your preferred editor.
Video Memory
By default, when you create a new Virtual Client, the video RAM is set to 16 MB as shown in Figure 1. For most Graphical User Interface Operating Systems (OS) 16 MB is inadequate.
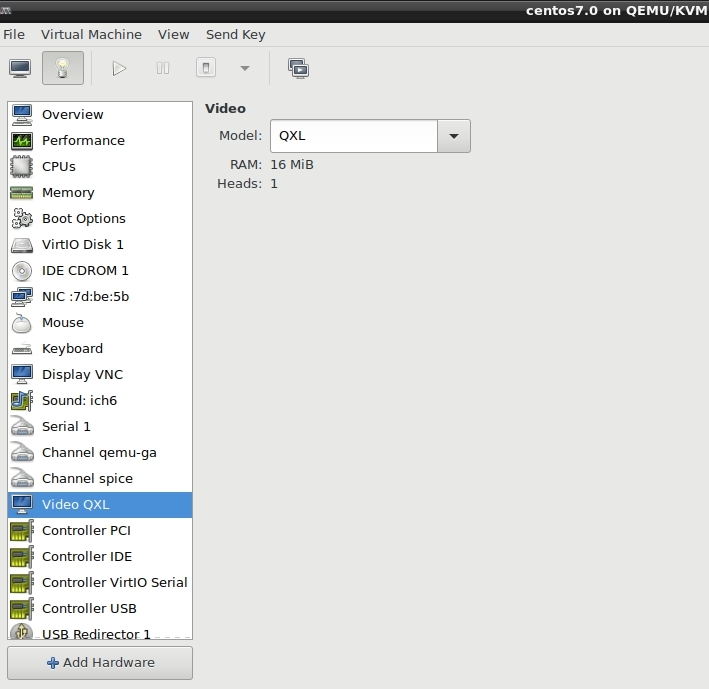
FIGURE 1
Some systems such as a Linux system with a higher end Desktop Environment will need more. Running Windows as a Virtual Client will need more as well.
So, how can the value be changed if there is not Graphical Interface for changing the value?
Every Virtual Client has an XML file which contains the information for that client. It is from these XML files that a client is loaded. To change the Video RAM of a client you only need to edit the XML file. You cannot easily edit the XML file outside of ‘virsh’ since the edits will sometimes be lost and will not take effect when the client is started.
Open a Terminal and type the command ‘virsh’. The Virtual Shell will open as shown in Figure 2.
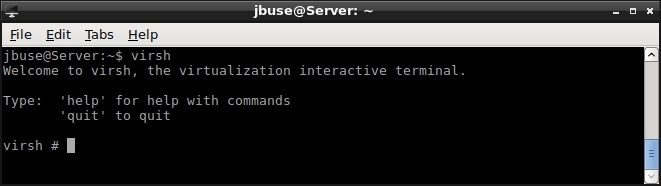
FIGURE 2
The next step is to get the names of any existing Virtual Clients by using the command ‘list --all’. In Figure 3 there is a list of my Virtual Clients. Once you know which client you wish to edit you can type ‘edit [client_name]’. For example, I can use my Virtual Client named ‘Sparky’ and type ‘edit Sparky’. Keep in mind that the Virtual Client name is case-sensitive. Once the command is entered the Virtual Client’s XML will be loaded into the default editor for ‘virsh’. Unless you previously changed the default editor it should be ‘vi’. Do not edit the XML of a running Virtual Client. The changes will not take effect until the client is restarted. It is best to make the changes while the client is off and then start the client when the edits have been made.
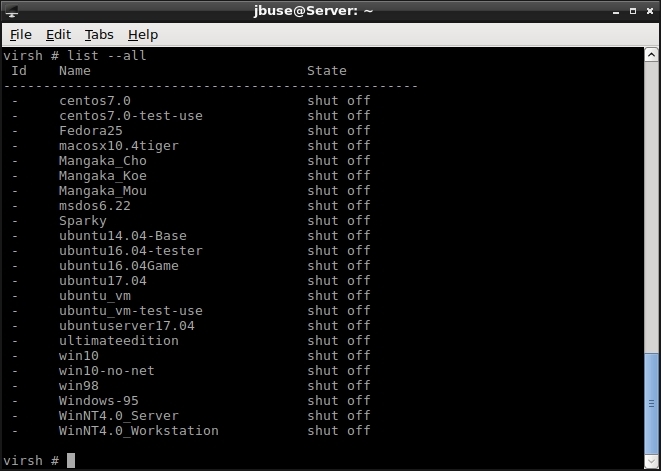
FIGURE 3
Once opened you should see the text of the XML in your default editor. Perform a server for ‘<video>’ and you should see text similar to that in Figure 4. Of course the editor may be different.
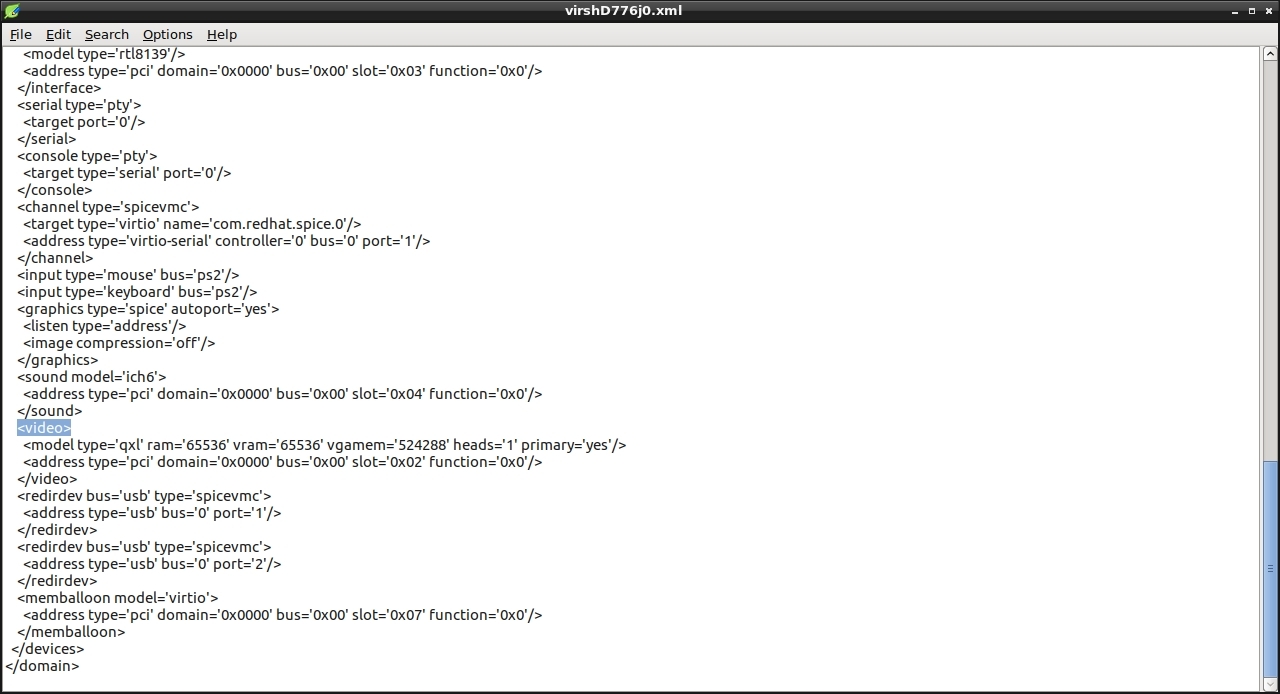
FIGURE 4
On the line after ‘<video>’ there is a portion titled ‘vgamem=’. Within the single quotes is the amount of Video RAM to use for the Virtual Client. The default should be ‘16384’ which is 16 MB. To find the amount you want to use take the amount of megabytes and multiply it by 1,024. The following lists the common Video RAM amounts:
If the number is not exactly divisible by 1024 then the amount will be rounded down to the next number divisible by 1024.
Save the XML file and close the editor. After the edits you can start the ‘Virt-Machine-Manager’ and then open the specified client. Once opened you can then click on the Hardware Details and look at the Video settings which should now show the changes you made. If you change the Video Type from QXL to Cirrus or any other change in the type the Video RAM settings will go back to 16 MB and need to be edited again.
Shutdown
Within a Virtual Client the OS can be shutdown from within the OS itself. With ‘virsh’ and ‘Virt-Manager’ you also close a Virtual Client.
To shut down a Virtual Client as if you pressed the power button on a physical system, otherwise known as a graceful shut down, use the command:
shutdown [vm-name]
The ‘vm-name’ is the name listed when you perform the command ‘list --all’ in ‘virsh’.
If you want to shut down the Virtual Client immediately, as if the system hardware failed or power was lost, then use the command:
destroy [vm_name]
For the graceful shut down to work the Virtual Client must have the Advanced Configuration and Power Interface (ACPI) enabled. To check if ACPI is enabled you need to open the specific client’s XML in the ‘virsh’ editor. Perform a search for the line ‘<acpi/>’. If the line is not found then you need to add it between ‘<features>’ and ‘</features>’. You also need to start the service with the command ‘/etc/init.d/acpid start’ from a Terminal.
Client doesn’t start
Sometimes a client will not start and no errors are reported. With any failure on a a Virtual Client you need to know what is going on ‘behind the scenes’ to solve the problem.
Every client has a log which holds the errors being generated. The location of the log files are at ‘/var/log/libvirt/qemu/’. The log files are named after the Virtual Client as listed in ‘virsh’. You will need to have ROOT privileges to view the log files.
Increase Storage Space
Sometimes when creating a new Virtual Client the initial storage space is not enough after items have been added and updates performed.
By default, the location of the image files for the Virtual Clients is in ‘/var/lib/libvirt/images/’. You will need ROOT privileges to access the folder and make changes to the files.
Open a Terminal and perform a ‘sudo su’. The type cd /var/lib/libvirt/images’.
Within the folder are the files named after the Virtual Clients. The file extension is ‘img’. To increase the storage size of an image perform the command:
qemu-img resize [vm_name.img] +[size]
The ‘vm_name’ is the name of the image or the same listed by the ‘virsh’ command. The Size is an amount followed by ‘GB’ for gigabytes.
For example, I wanted to increase the storage size of a Virtual Client named ‘Ubuntu’ by 5 GB, the command would be:
qemu-img resize Ubuntu.img +5GB
When you restart the Ubuntu Virtual Client you will need to use ‘gparted’ or another similar program to extend the current disk partition.
I hope this can help you get around libvirt more easily and ‘fix’ issues you may have.
Installation - https://www.linux.org/threads/virtualization-–-libvirt.4496/
GUI - https://www.linux.org/threads/virtualization-–-libvirt-gui.4497/
This article will cover more details of the configuration on various topics that aren’t obvious to set.
‘virsh’
The way to change some underlying settings for a Virtual Client is to use ‘virsh’. The command ‘virsh’ is run from a Terminal.
Once you start ‘virsh’ then you are in the ‘virsh’ editor. When editing the Virtual Client settings the default editor is ‘vi’, but this can be changed to your personal preference.
Let’s say you want the default editor to be ‘leafpad’. The command to run would be:
export EDITOR=leafpad
NOTE: When you reboot the system then the setting reverts back to the default.
Let’s make the default permanent. To make the settings permanent we need to have the environment variable set at boot time.
Open a Terminal and type the command ‘sudo leafpad /etc/environment’. Change the editor from ‘leafpad’ to your preferred editor by replacing the command to start the editor. Once the ‘environment’ file is opened you need to go to the last line and enter ‘EDITOR=leafpad’. Again, change the editor name to your preferred text editor. Save the changes and close the editor.
To make the settings take effect immediately and not require a reboot enter the command ‘source /etc/environment’.
Now you can execute the command ‘echo $EDITOR’ to see that the entry is set to your preferred editor.
Video Memory
By default, when you create a new Virtual Client, the video RAM is set to 16 MB as shown in Figure 1. For most Graphical User Interface Operating Systems (OS) 16 MB is inadequate.
FIGURE 1
Some systems such as a Linux system with a higher end Desktop Environment will need more. Running Windows as a Virtual Client will need more as well.
So, how can the value be changed if there is not Graphical Interface for changing the value?
Every Virtual Client has an XML file which contains the information for that client. It is from these XML files that a client is loaded. To change the Video RAM of a client you only need to edit the XML file. You cannot easily edit the XML file outside of ‘virsh’ since the edits will sometimes be lost and will not take effect when the client is started.
Open a Terminal and type the command ‘virsh’. The Virtual Shell will open as shown in Figure 2.
FIGURE 2
The next step is to get the names of any existing Virtual Clients by using the command ‘list --all’. In Figure 3 there is a list of my Virtual Clients. Once you know which client you wish to edit you can type ‘edit [client_name]’. For example, I can use my Virtual Client named ‘Sparky’ and type ‘edit Sparky’. Keep in mind that the Virtual Client name is case-sensitive. Once the command is entered the Virtual Client’s XML will be loaded into the default editor for ‘virsh’. Unless you previously changed the default editor it should be ‘vi’. Do not edit the XML of a running Virtual Client. The changes will not take effect until the client is restarted. It is best to make the changes while the client is off and then start the client when the edits have been made.
FIGURE 3
Once opened you should see the text of the XML in your default editor. Perform a server for ‘<video>’ and you should see text similar to that in Figure 4. Of course the editor may be different.
FIGURE 4
On the line after ‘<video>’ there is a portion titled ‘vgamem=’. Within the single quotes is the amount of Video RAM to use for the Virtual Client. The default should be ‘16384’ which is 16 MB. To find the amount you want to use take the amount of megabytes and multiply it by 1,024. The following lists the common Video RAM amounts:
- 32 MB – 32768
- 64 MB – 131072
- 128 MB – 131072
- 256 MB - 262144
- 512 MB – 524288
- 1 GB – 1048576
If the number is not exactly divisible by 1024 then the amount will be rounded down to the next number divisible by 1024.
Save the XML file and close the editor. After the edits you can start the ‘Virt-Machine-Manager’ and then open the specified client. Once opened you can then click on the Hardware Details and look at the Video settings which should now show the changes you made. If you change the Video Type from QXL to Cirrus or any other change in the type the Video RAM settings will go back to 16 MB and need to be edited again.
Shutdown
Within a Virtual Client the OS can be shutdown from within the OS itself. With ‘virsh’ and ‘Virt-Manager’ you also close a Virtual Client.
To shut down a Virtual Client as if you pressed the power button on a physical system, otherwise known as a graceful shut down, use the command:
shutdown [vm-name]
The ‘vm-name’ is the name listed when you perform the command ‘list --all’ in ‘virsh’.
If you want to shut down the Virtual Client immediately, as if the system hardware failed or power was lost, then use the command:
destroy [vm_name]
For the graceful shut down to work the Virtual Client must have the Advanced Configuration and Power Interface (ACPI) enabled. To check if ACPI is enabled you need to open the specific client’s XML in the ‘virsh’ editor. Perform a search for the line ‘<acpi/>’. If the line is not found then you need to add it between ‘<features>’ and ‘</features>’. You also need to start the service with the command ‘/etc/init.d/acpid start’ from a Terminal.
Client doesn’t start
Sometimes a client will not start and no errors are reported. With any failure on a a Virtual Client you need to know what is going on ‘behind the scenes’ to solve the problem.
Every client has a log which holds the errors being generated. The location of the log files are at ‘/var/log/libvirt/qemu/’. The log files are named after the Virtual Client as listed in ‘virsh’. You will need to have ROOT privileges to view the log files.
Increase Storage Space
Sometimes when creating a new Virtual Client the initial storage space is not enough after items have been added and updates performed.
By default, the location of the image files for the Virtual Clients is in ‘/var/lib/libvirt/images/’. You will need ROOT privileges to access the folder and make changes to the files.
Open a Terminal and perform a ‘sudo su’. The type cd /var/lib/libvirt/images’.
Within the folder are the files named after the Virtual Clients. The file extension is ‘img’. To increase the storage size of an image perform the command:
qemu-img resize [vm_name.img] +[size]
The ‘vm_name’ is the name of the image or the same listed by the ‘virsh’ command. The Size is an amount followed by ‘GB’ for gigabytes.
For example, I wanted to increase the storage size of a Virtual Client named ‘Ubuntu’ by 5 GB, the command would be:
qemu-img resize Ubuntu.img +5GB
When you restart the Ubuntu Virtual Client you will need to use ‘gparted’ or another similar program to extend the current disk partition.
I hope this can help you get around libvirt more easily and ‘fix’ issues you may have.
Last edited:

